Apple devices, in general, and the iPhone, in particular, are known to be much more secure than Android devices. But that is only true to some extent. The closed development mode and timely updates make the iPhone one of the most secure smartphones. However, there are times when even your iPhone is hacked, and maybe someone is accessing your iPhone remotely without your knowledge. So, How to find out if someone is accessing your iPhone remotely?

The best way to find out if someone is accessing your iPhone remotely is to find the unrecognized devices under your Apple ID. Simply sign in to your Apple account and sign in with your Apple ID. Scroll down and check the unrecognized devices, if any. If you find any such device, it may be an indicator to show that your iPhone is hacked.
Remote Access to iPhone – What Does It Mean?
Your iPhone or any iOS device may be controlled through unauthorized access to your Apple account. This will provide the hacker complete access to everything on your phone. It can provide the hacker full access to your hidden passwords and credentials. This can severely affect you personally and financially since you may have personal and financial data saved on the phone. And, since the hacker has access to your Apple account, he can access all the data that is backed up on iCloud. Although this gives them access to your data, it is not remote access actually. Remote access is something in which someone else gain access, and control your device as they wish
Remote access to an iPhone can be achieved through a few unauthorized methods, such as hacking or exploiting the vulnerabilities that may be present in the iPhone’s security. It may also be enabled through legitimate methods such as remote device management by an employer or parental control applications.
Above all, when you make mistakes by clicking on links that you get via text or sometimes, you get some social media invoice, and you click on that, and do some further activity like giving some permissions, and all. These actions of yours may help hackers gain remote access to your device as well.
Can Someone Access My iPhone Data From Another Device?
If someone has only your Apple ID, he or she may not be able to access your iPhone data. However, if they have both your Apple ID and password, they will easily be able to access your iPhone data that is backed up on iCloud. The best way to prevent this is to use a two-factor authentication.
But, as I said, accessing your iCloud data is something else and controlling your iPhone remotely is different thing.
How to Tell if someone is accessing your iPhone remotely?
Well, as I already said, remote access means someone else is controlling your iPhone, and he is able to use the phone the way you use it. That is what remote access is. But, how would you know whether your iPhone is being used by someone else remotely?
Here are a few pointers that you consider to find out whether your iPhone is remotely controlled:
A Faster Data Usage
If you find that your iPhone has faster data usage even when you are not doing something data-intensive, that can be an indicator that your phone is being accessed remotely by someone, and the data is being used.
If your iPhone has spyware installed, it will not differentiate between what to send and what not to. It simply transfers every data on the phone to the destination. If you are running out of your data without doing much, it is time you investigate the reasons as soon as possible in order to safeguard yourself.
Unusual Battery Usage
If you notice your iPhone battery is running out really fast without even you using it much, it can be another hint to show someone else is accessing your iPhone remotely. This can be large because of a huge number of unauthorized apps running in the background on your phone.
However, if you are into power-hungry applications and operations yourself, the battery drain may not be a serious concern. If not, investigate the reasons for the faster battery drainage.
Warm Battery in Sleep Mode
It is normal for your battery to get hot in certain circumstances. A few examples can include playing a game or using your phone for a long time. However, if you find it getting hot even when it has the screen turned off or is in sleep mode – that should indicate something is amiss.
If you notice that your phone is heating up when in sleep mode, it means your phone CPU is under use. Make sure that your phone does not have spyware installed, which provides remote access to your iPhone.
Slower Performance of the Phone
All the above causes – huge data usage, unauthorized apps, and unusual CPU activity – can result in making your iPhone show a slower performance. You would find your iOS apps lagging or taking a lot of time to load. It may also be noticed that your phone shuts down at times without any warning.
Strange and Unusual Notifications
Receiving unusual and unidentified notifications and emails can also be an indicator to show that your phone has been hacked. A good example is a push notification that appears out of nowhere, even when you have closed your browser. There may be a few other notifications that you might have never been expecting.
Unauthorized Password Changes
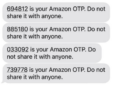
Did you receive any password change notifications even when you have not initiated any sort of password change? This is yet another possible sign that someone is remotely accessing your iPhone. You may get locked out of your accounts all of a sudden or may receive a password change notification when you have not changed it. Using two-factor authentication as an extra layer of security is yet another practical option.
If Someone Has My Apple ID, Can They See My Texts?
If anyone has your Apple ID, they can see your text and messages on all synced devices. In addition to the text, they can also view your location, iMessage, text messages, iCloud content, photos, and contacts.
However, they will need to sign in to be able to get your WhatsApp messages. For this to happen, they will need to have your Apple ID and password. If you have shared your password with someone, it is high time you changed it.
How to stop someone from accessing your phone remotely on your iPhone?
To prevent someone from accessing your iPhone remotely, you can follow the steps and ideas below:
Never Leave Your Phone Unattended
Never leave your phone anywhere unattended. If you have to leave your phone somewhere as part of the security checkups and other requirements, make a habit of turning the screen off. This will ensure that no one will have access to your Apple ID or other security options on your iPhone.
Use VPN on Public Networks
When you are on a public network, make sure that you are using a VPN service. In fact, public WiFi networks are the hotspot for hackers to unleash terror. If you have to use a public network for any reason, you can consider using a VPN service of your preference.
Use of VPN will ensure that You will be safer and secure against adware, malware, spyware, and hackers. Also, learn to turn off WiFi or Bluetooth when you are in public networks. Hackers tend to use the public hotspots to remotely access your iPhone.
Check Your App Permissions
When you install an app on your device for the first time, make sure that you have provided only those app permissions that are required. Ensure that you have given the app permission only for the apps that you trust.
Apart, you need to ensure that all your apps are downloaded from the app store only. Never download and install apps from any other third-party sources. If you are not sure about any app, you can get in touch with Apple support for clarification.
Keep Your Device Updated
Updated software is what ensures a success rate that is higher in safeguarding your privacy and security. The software updates on iOS are not merely about adding new features. They are more about patching the security loopholes that might have appeared in your device.
Make sure that you have updated your phone as and when the updates are made available. You can also consider uninstalling the apps installed on your iPhone that you do not trust and do not use at all. The unfamiliar apps are a sign of severe concern.
Change Your Passwords Regularly
Changing your passwords at regular intervals can be a great security patch you can apply. Changing the password for Apple ID can help you in lowering the possibility of someone accessing your iPhone remotely. Make sure to use difficult passwords. These can include an alphanumeric mix with capitalized characters and special symbols.
The Closing Thoughts
Apple promises a considerable level of security when it comes to its users and its operating system. However, despite the powerful security that an iPhone is known to offer you, hackers do tend to get access to your phone and access your iPhone remotely. We have pinpointed the best ways that can help you find out if someone is accessing your iPhone remotely. Analyze them, and if you have any such issues on your phone, make sure to raise the red flag immediately.
FAQs
How do I check if my iPhone is linked to another device?
The perfect way to check if your iPhone is linked to another device is to go to your Apple ID and check the devices associated with your Apple ID. If you find any unrecognized device, make sure to remove it. It is a clear sign that someone is accessing your iPhone remotely. Also, change your Apple ID password immediately.
Can someone get into my iPhone without me knowing?
Yes, hackers and scammers can access your iPhone without your knowledge through the vulnerabilities in your iOS version or the loopholes in the app. Hackers may even trick you and gain access to your iPhone without you knowing.
Can iPhones Be Hacked?
The iPhones are more secure than Android devices. However, they can be hacked, but the possibility is quite rare. Hackers can exploit the security loopholes in the iOS system and thus gain unauthorized access to your iPhone.















Add Comment