A data breach is an attack on personal information stored on a computer system. Organizations and individuals are targets for data breaches, and the stats are concerning. The US is the country with the most people affected by data breaches, along with Russia. But, no matter where you are, there is always a chance you will become a target.
I have been running a business for more than a decade now, and mostly I work with websites. I have faced hacker attacks so many times, and have been trying to tighten the security of my websites. Not just websites but it is quite important for me to keep my Macbook also safe because it is what I use to access all of my websites, servers, and all the transactions are done by this system only. So, keeping it safe is of utmost importance.

Working for so long, I have learned and gotten to know various tips and tricks to secure my websites and my computers as well. In this article, I am going to share some of the best tips to stay safe from a data breach.
So, here I am sharing some tips that will save you from the most common attack vectors for data breaches:
Online Security Tips to Stay Safe from Data Breach
Tips for Phishing
Phishing is a social engineering attack where adversaries try to gather information from victims or infect a system through malicious emails. These emails usually include demanding messages intended to instill fear and panic in the victim or a harmful attachment that will spread malware on the victim’s computer. Attackers sometimes try to imitate a person the victim knows to increase their chances of success. I have shared my experience of such a threatening email earlier which was obviously a phishing email.

Here is how to recognize and protect against phishing:
- Avoid clicking on links or attachments in emails from unknown senders.
- Verify the identity of the sender.
- Misspellings and poor grammar are common signs of phishing.
- Ignore requests for personal information like a social security number, bank information, etc.
- The message is unexpected and unsolicited, and coming from someone you rarely deal with.
- The link included in the email takes you to a page asking you to enter credentials.
Tips for Weak, Stolen, or Compromised credentials
Credentials are your username and password on each website or platform you use. If an attacker has these two pieces of information, they can access your account and everything it contains. Even prominent security technologies like multi-factor authentication (MFA) aren’t perfect. The most common way attackers steal credentials is through phishing.
Here are some ways to protect your accounts:
Use a Password Manager
Managing many different accounts is challenging. Many people use weak passwords or the same password for every account. A password manager is a great way to address this issue. Password managers can generate strong passwords that are almost impossible to crack and store them securely in a personal vault. If you don’t have access to a password manager for any reason, you must use a different password on different websites you log in to. Also, it is observed that passwords that are long and use various special characters are less likely to be compromised as compared to weak passwords. Thus, choose a strong password whenever you signup to any website.
Use 2-factor authentication
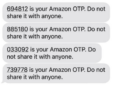
Multi-factor authentication isn’t 100% perfect, but it will significantly reduce the chances of a breach. Authenticator apps are free – all you have to do is install them and link them to your accounts. You will then have to confirm it’s you each time you log into an account. Theoretically, the only way a hacker can bypass this is by having physical access to your device. In fact, nowadays, most of the services are offering 2-factor authentication so you may not need any such authenticator apps. For example, Gmail, Facebook, and many more sites are already offering 2-factor authentication
Tips for System Vulnerabilities
Another common attack vector that leads to a data breach is system vulnerabilities. Vulnerabilities are weaknesses in an IT system that an attacker can exploit to gain unauthorized access or do harm in another way. Attackers often have to combine multiple vulnerabilities to breach a system successfully. Zero-day vulnerabilities are the most dangerous because the people responsible for their mitigation don’t know it exists.
System vulnerabilities are largely out of your control. One thing you can do to ensure protection is to always update your system and software to the latest version. Hackers and security teams are always racing to discover and fix vulnerabilities. That’s why updates and patches are so common. Not installing these updates leaves many known vulnerabilities hackers can exploit to breach your system. Above all, I would recommend using any good Antivirus or internet security software to block viruses or malware.
Tips for Man-in-the-middle (MITM) attacks
A man-in-the-middle attack is when the attacker intercepts messages between two parties to gather information or tamper with communication. The attack begins with a criminal gaining access to an IT network, allowing them to intercept a victim’s online activities before they reach their intended target. Since victims aren’t aware of the man-in-the-middle, the attacker can do damage for weeks or months without getting caught.
To stay away from the man in the middle:
- Ensure a secure connection: Only visit websites with an HTTPS connection and avoid using public Wi-Fi as it’s usually unprotected. Nowadays, public wifi is very common but prefer not to use them. Your phone’s mobile data is safer than that of public Wifi.
- Install a VPN: this will encrypt the data you send online. Even if a hacker breaches your network, they cannot read the encrypted data.
- Enable multi-factor authentication (MFA): If a man-in-the-middle tricks you and obtains your credentials, you can still stop them with MFA.
Bonus tip: Choose Your Apps Wisely
Only download apps from trusted sources: the App Store for iOS and the Google Play Store for Android devices. Even there, read reviews and try to only install apps with a good reputation. Even globally popular apps can have shady practices.
Final Thoughts
These were some of the main attack vectors hackers use in data breaches. There are many other threats, but most of the tips in this article will also apply to them. The main points are to secure your accounts with strong passwords and MFA and be mindful of clicking on links and attachments in suspicious emails or text messages.















Hello, Atish sir very useful and unique Post.
please keep sharing your valuable advice with us.
thanks,
Thank for visiting, Sunaina.