Our technological world has become critical to the smooth running of society. Most people use the internet to make purchases and other financial transactions daily, and a constant stream of sensitive data flows through our devices. Such data has become a goldmine of valuable information for cybercriminals. The need for security will never disappear. However, technological advances offer better ways to combat these threats. Here we discuss how to best use technology to improve your online security.
Cybersecurity Tools
Luckily, as criminals advance, so do the systems that protect them. For example, VPNs that hide your IP address from potential hackers and keep your online activity private have become more widely used as a valuable everyday security tool. Data analysis and artificial intelligence have also greatly improved cyber security. These technologies have led to analyzing user behavior and systems that learn your habits. No two people use technology in the same way. Therefore, user behavior analysis can differentiate between people based on their actions.
Installing suitable antivirus software has long been the first step to computer and online security, and there is now a wide range of security products on offer. Do all software packages do the same things? You may wonder if all software packages offer the same security, or are they all the same?
The most comprehensive antivirus software usually includes anti-spyware, anti-phishing, search result filtering, firewall, webcam protection, application behavior monitoring, and sensitive file monitoring in addition to antiviruses. It would be advisable if you also considered antivirus software that offers protection for social networks, parental controls, an anti-theft program in case of a lost device, and a password manager.
One of the technologies I found that helps you login to multiple web applications securely. You can Discover how to leverage the power of SAML (Security Assertion Markup Language) to enhance your online security.
One costly mistake many people make is taking the time and effort of choosing and installing an antivirus program but ultimately failing to keep it updated. As Norton mentioned here, keeping your software updated is vital because each new version has features that address progressive cybersecurity threats, giving you improved and comprehensive security.
 Source: Pixabay
Source: Pixabay
Email is still a powerful tool and the means by which most of us communicate daily, and, as we’ve addressed in a previous article on TechTricksWorld, email is especially critical for business and marketing. Using software to check that emails are deliverable means you reduce the unnecessary expenditure of sending newsletters and emails. The email verification tool helps improve security, protecting you from phishing scams. Verification tools also make all the difference in the performance of an advertising or marketing campaign by verifying and validating the recipients’ email addresses. For instance, this email verification software from Seon automatically checks if an email address is valid or not and is frequently used by marketers and sales teams to ensure emails are received. This suave email verification software also helps collect more valuable information about email addresses, including social media usage, which is incredibly useful for fraud prevention. You can quickly gather data, including whether or not an email is in use and how long it has been active, or check if an email is connected to a social media profile, helping verify whether this is an authentic user or a fake account.
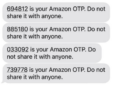
In addition, two-step verification is a simple and effective way to protect your account and your password. It is, therefore, the second vital layer of security for your data. Its advantage is that it uses a device that you alone physically hold. For example, you can require that every time you try to log in to your account again, a four-digit confirmation code is sent to your phone. As Al Jazeera reports in this article, this is a great way to stop hackers who might have managed to crack your password as they don’t also have access to your phone. Microsoft is offering this two-step security option along with many other online service providers.
Social Media Security
Another vital consideration to protect yourself and improve your online security is how much personal information you share on your social media profiles, such as Snapchat and Instagram. The information people are willing to post online varies, whether it’s your name, marital status or location, age, job title, etc. You may re-examine what you are sharing about yourself on social media if you know that a hacker could catalog this information and put it into a spreadsheet containing millions of pieces of data to be later sold.
These databases that hackers can utilize are not created by breaking into social network servers or websites but are primarily built by taking the social media platforms’ data accessed by the public. Bad actors use automated programs to grab all the freely available information about users. In theory, most of the data compiled can be found by simply browsing the profile pages of social networks.

Source: Pixabay
In just one incident in 2021, a hacker sold another database containing around 500 million records extracted from LinkedIn. Most social networks offer application programming interface (API) partnerships, which allow other companies to access their data, for example, for marketing purposes or to build applications. Many believe that API programs, which give more information about users than the general public can see, should be more closely monitored.
When this information is in the wrong hands, it could have significant consequences, including vulnerability to phishing scams. You can do some simple things to protect yourself when using social media, like carefully reading media site terms and not sharing personal information like address or even your full name. Creating strong private, secure passwords is also vital.
Use a trusted password manager. Effective password manager tools and programs are not just crucial for social media use but all online activity. Even simply, technology can help you improve your social media security. Suppose you use similar login and password credentials for different accounts and sites. In that case, it means that once a hacker gains access to one account, it opens the door to all your online activity, including valuable online banking details or other sensitive personal data.
Conclusion
As the landscape of cyber security changes, the security tools and techniques are constantly evolving, and so is the technology. Innovations are moving so fast these days that it won’t be long before high-end security technology is a thing of the past. Future improvements will make online security technologies faster and more reliable.















Add Comment